Introduction
Has your computer been encrypted and locked by Petya ransomware? Don't worry — this guide will help you decrypt your system, repair your MBR, and restore your PC without antivirus tools or external help.
Petya is an MBR-based ransomware, meaning:
- It encrypts your disk sectors
- It overwrites your Master Boot Record
- It replaces your Windows bootloader with a ransom screen
- It prevents Windows from booting at all
This guide will help you decrypt Petya safely and restore your PC back to normal.
Do NOT run malware on a real computer. All demonstrations on ArsenTech are performed inside safe, isolated virtual machines. Follow the steps carefully — bootloader repair and decryption are sensitive. NEVER trust instructions written by a ransomware!
If you prefer watching instead of reading, here's the full video guide: Watch the video on YouTube
Step 1 - Preparing to decrypt the PC
Download the PetyaDecryptor made by security researcher @hasherezade: https://github.com/ArsenTech/downloads/blob/static-files/PetyaDecryptor.zip
- On a clean PC, open the
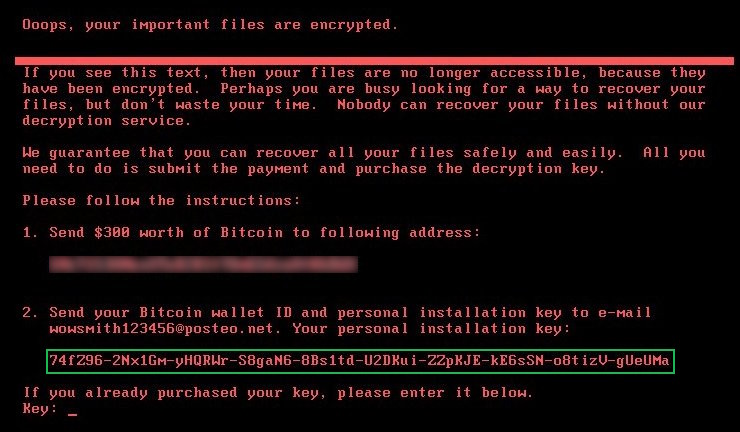
id_raw.txtfile included in the ZIP. - On the infected PC, copy the green-outlined Petya ID from the ransom screen.
- Type the ID exactly, with:
- No spaces
- No hyphens (
-) - Only the raw characters
Do NOT copy the decryption ID from screenshots or online posts. Petya generates a unique ID per device — using the wrong ID will NOT decrypt your computer.
Step 2 - Generating the Key
- Save the edited
id_raw.txtfile. - Drag
id_raw.txtontopetya_key.exe. - Select your Petya variant:
r→ Original Petya (Red Screen)g→ Mischa / Green Petyad→ GoldenEye
- The decryptor will display the correct decryption key for your infected PC.
If the decryptor fails, double-check your ID formatting. Even one incorrect character will produce a wrong key.
Step 3 - Decrypting Petya
On the infected PC:
- Type the generated key on the ransomware screen
- Press Enter
If everything is correct, you will see:
Decrypting sector X of Y (XX%)
Once decryption reaches 100%, Petya will show:
Please reboot your computer!
Restart your computer.
If Windows boots, congratulations! You removed Petya from the PC. If not, continue to Step 4.
Step 4 - If the MBR fix failed
TSometimes the disk decrypts successfully but the bootloader remains broken. This section handles those “hard cases.”
4.1 — Basic Fix (Startup Repair)
You need:
- A clean PC
- A USB flash drive
- A Windows ISO
- Rufus / Ventoy
Steps
- Create a Windows installation USB
- Boot the infected PC from the USB
- Click Next → Repair your computer
Navigate to:
Troubleshoot → Advanced Options → Startup Repair
Startup Repair may take several minutes. This is normal, so be patient :-)
If the PC boots afterward → done. Otherwise, continue.
4.2 — Run Bootrec Commands
Boot again from the USB:
Next → Repair your computer → Troubleshoot → Advanced Options → Command Prompt
Run:
bootrec /fixmbr
bootrec /fixboot
bootrec /rebuildbcdIf all commands succeed → restart. If Access Denied or no OS found, continue.
4.3 — Check that Partitions Still Exist
diskpart
list vol
If your Windows volume:
- Is NTFS
- Has the correct size
Continue to the next step. If it appears RAW, missing, or incorrect → skip to Step 4.6.
4.4 — Try Rebuilding BCD Without bootrec
Try bypassing bootrec entirely:
bcdboot C:\Windows /f ALLIf the PC boots → fixed! Otherwise, continue.
4.5 — Recreate the MBR Manually (Legacy BIOS Only)
Only for Legacy BIOS systems. Do NOT perform these steps on UEFI computers.
diskpart
list disk
select disk 0
list partition
select partition X :: likely the 100 - 500MB System Partition
active
exitThen repair:
bootsect /nt60 sys /mbrRestart. If it's still broken → continue.
4.6 — Use TestDisk to Recover the Partition Table
Download TestDisk (on a clean PC): https://www.cgsecurity.org/Download_and_donate.php/testdisk-7.2-WIP.win.zip
Open TestDisk from the Windows Recovery USB. Path:
TestDisk → No Log → Select Disk → EFI GPT → Analyze → Quick Search → Write
- Select the partition containing your Windows folders
- Press Write
- Confirm with Y
If this succeeds → reboot. If not → final stage.
Final Stage — When Nothing Works
Petya may cause bootloader/system partition damage that cannot be reversed unless decrypted correctly.
Reinstallation is required if:
- The Windows partition is RAW
- The BCD cannot be rebuilt
- The MBR/EFI are corrupted beyond repair
- The Windows partition is missing
- TestDisk cannot rebuild the NTFS boot sector
At this point:
- Recover your files (TestDisk, Linux live USB, or Windows PE)
- Back everything up
- Reinstall Windows
Conclusion
And that's it! You've successfully removed the Petya ransomware, decrypted your system, and restored the bootloader. Petya is extremely destructive — it encrypts data at the sector level and corrupts the MBR, so fixing the PC manually is essential.
To prevent future infections:
- Delete suspicious .exe files immediately
- Never run unknown programs
- Use a stronger antivirus
- Keep real-time protection enabled
- Always use a virtual machine for malware testing
- Avoid downloading from untrusted sources
- Back up your important files regularly!
Thanks for reading! If you want more malware removal guides and educational malware tests, check out my YouTube channel.
GitHub @ArsenTech · YouTube @ArsenTech · Patreon ArsenTech · ArsenTech's Website